Creating Custom Security Policies
This guide explains how to create your own organization-specific security policies using the AI Security Gateway's web interface.
Policy Quick Start
The gateway provides three ways to create custom policies:
- Use a Template - Start with pre-configured templates and customize
- Use the Pattern Library - Add pre-built patterns to new or existing policies
- Build from Scratch - Create completely custom policies using the Policy Builder
All policy creation and management is done through the web interface - no file editing required.
Method 1: Create from Template
The fastest way to create a custom policy is to start with a template.
Access Templates
- Navigate to Policies → Templates tab
- Browse available templates by type (MCP, LLM, Both)
- Use the search bar to filter templates by name or description
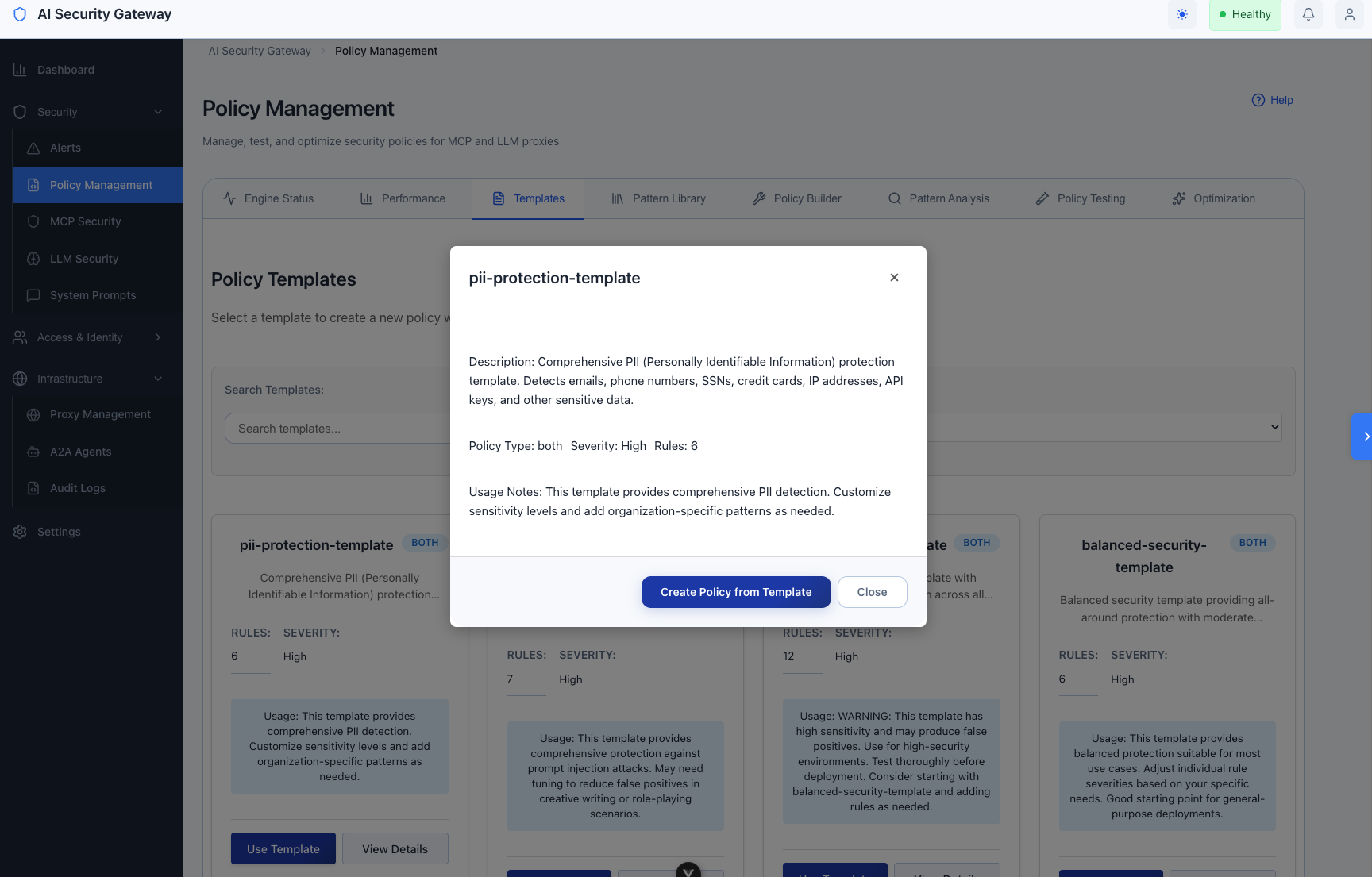
Select and Customize Template
Review template details:
- Click View Details to see template contents
- Review rule count, severity level, and usage notes
Use the template:
- Click Use Template button
- The Policy Builder opens with pre-filled form
Customize the template:
- Edit Policy Name (required) - e.g., "acme-corp-security"
- Select Policy Type (MCP, LLM, or Both)
- Update Description to match your use case
- Set Severity and Version
- Modify rules, patterns, and redaction settings as needed
Save your policy:
- Click Validate to check policy structure
- Click Save Policy to create your custom policy
Method 2: Use Pattern Library
Add pre-built detection patterns to new or existing policies.
Access Pattern Library
- Navigate to Policies → Pattern Library tab
- Browse categories:
- PII Detection - Patterns for personally identifiable information
- Toxicity Detection - Patterns for toxic/harmful content
- Prompt Injection - Patterns for prompt injection attacks
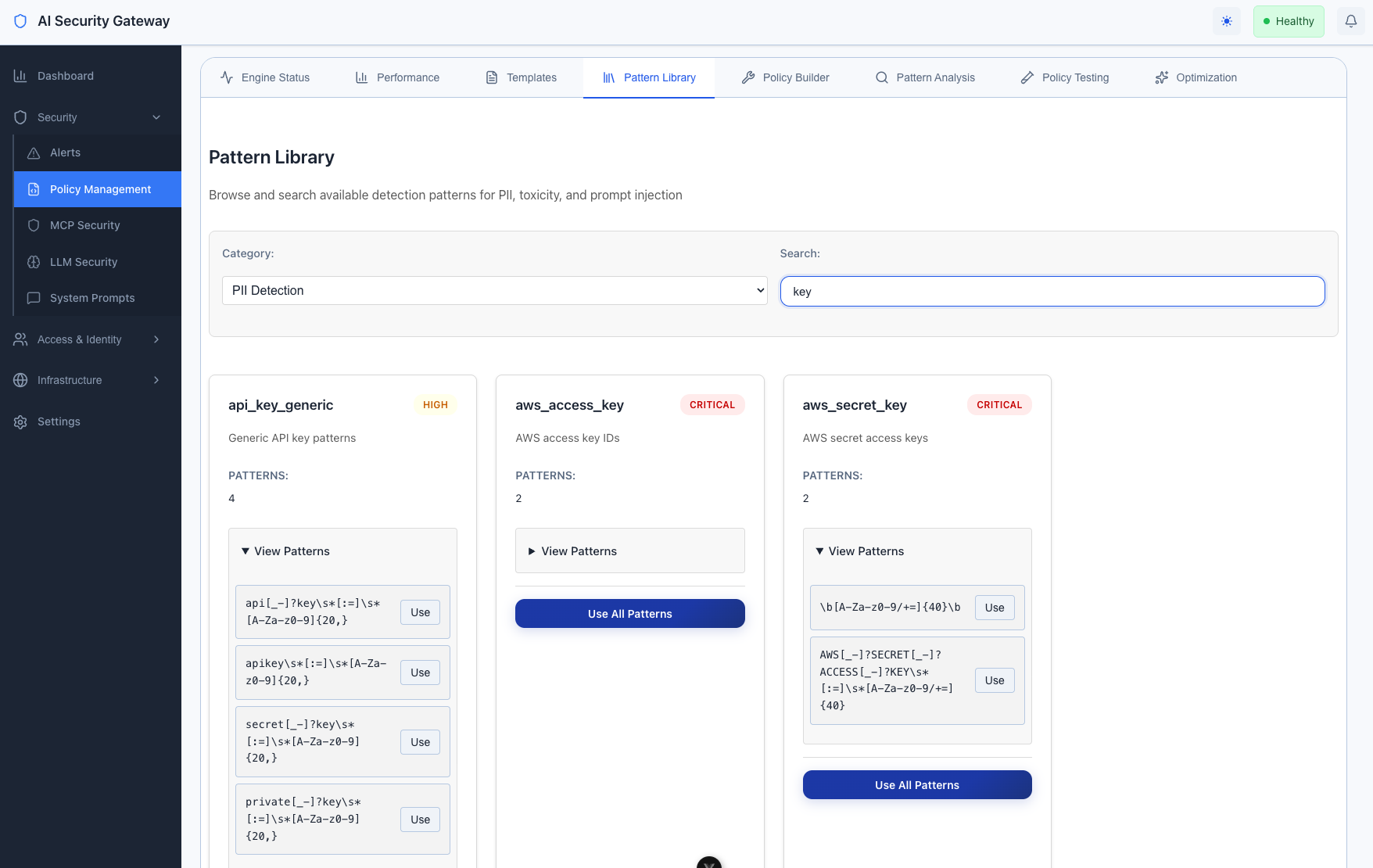
Add Patterns to Your Policy
Adding Individual Patterns:
- Browse patterns in your desired category
- Expand pattern details by clicking "View Patterns"
- Click "Use" next to a specific pattern
- Pattern is automatically added to your policy's last rule
Adding All Patterns from a Category:
- Find the category you want (e.g., PII Detection)
- Click "Use All Patterns" button on the category card
- All patterns from that category are added to your policy
Pattern Library Categories:
- PII Detection: Email addresses, phone numbers, credit cards, SSNs, IP addresses, etc.
- Toxicity Detection: Hate speech, profanity, harassment, threats
- Prompt Injection: Jailbreak attempts, system prompt manipulation, role confusion
Method 3: Build from Scratch
Create a completely custom policy using the Policy Builder.
Access Policy Builder
Option 1: From MCP/LLM Security Pages
- Navigate to MCP Security or LLM Security page
- Click + Create Policy button
- Policy Builder modal opens
Option 2: From Policies Page
- Navigate to Policies → Policy Builder tab
- Start configuring your policy
Policy Builder Form Fields
Policy Builder Form Fields
The Policy Builder is organized into four main sections:
1. Basic Information Section
Policy Name (required)
- Unique identifier for your policy
- Example: "acme-corp-security", "finance-dept-policy"
Policy Type (required)
- MCP: For Model Context Protocol servers
- LLM: For Large Language Model APIs
- Both: For policies that work with both types
Description
- Explain the purpose of your policy
- Example: "Security policy for ACME Corp - Protects employee IDs and internal API keys"
Severity
- Low, Medium, High, or Critical
- Sets the baseline severity for this policy
Version
- Track policy versions (e.g., "1.0", "2.1")
2. Security Rules Section
Add detection rules to identify threats and patterns.
Per-Rule Fields:
- Rule ID: Unique identifier (e.g., "COMPANY_001")
- Rule Name: Descriptive name (e.g., "Employee ID Detection")
- Category: Type of security check (e.g., "Data Protection")
- Severity: Low, Medium, High, or Critical
- Description: What this rule detects
- Patterns: One regex pattern per line (multi-line supported)
Example Rule:
Rule ID: COMPANY_001
Name: Employee ID Detection
Category: Data Protection
Severity: Medium
Description: Detect company employee ID patterns in traffic
Patterns:
\b(EMP|EMPL)[-_]?\d{6}\b
\b[A-Z]{2}\d{6}\bAdd/Remove Rules:
- Click + Add Rule to create a new rule
- Click Remove to delete a rule
3. Blocked Patterns Section
Define patterns that should be immediately blocked.
Per-Pattern Fields:
- Pattern (required): The pattern to block
- Severity: Low, Medium, High, or Critical
- Action:
block,warn, orlog - Reason: Why this pattern is blocked
Example Blocked Pattern:
Pattern: \bdrop\s+table\s+company_data\b
Severity: Critical
Action: block
Reason: Attempted access to protected company data tableAdd/Remove Patterns:
- Click + Add Blocked Pattern to create a new pattern
- Click Remove to delete a pattern
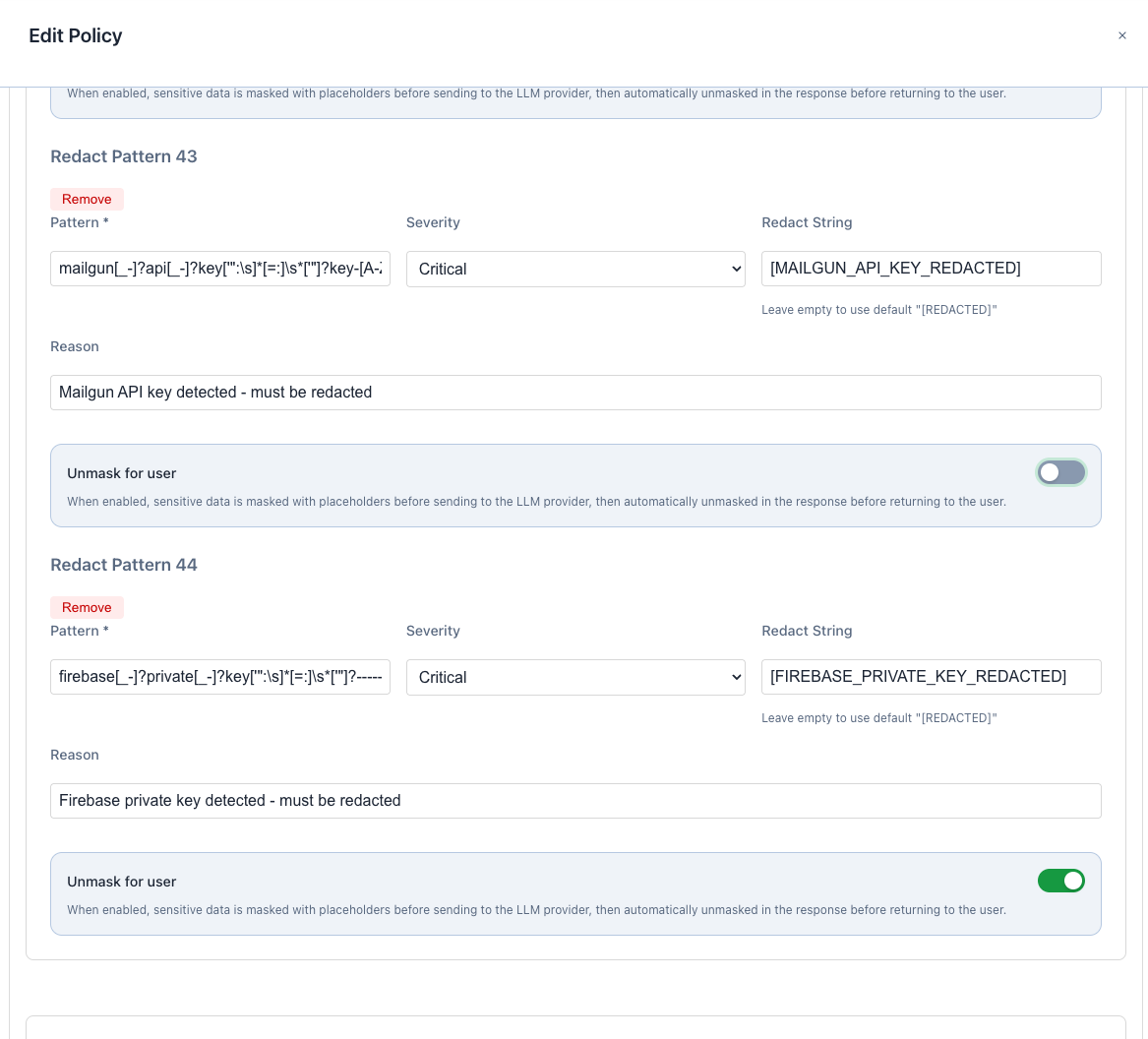
4. Redact Patterns Section
Define patterns that should be redacted (replaced) rather than blocked.
Per-Pattern Fields:
- Pattern (required): The pattern to redact
- Severity: Low, Medium, High, or Critical
- Redact String: Replacement text (default: "[REDACTED]")
- Reason: Why this pattern is redacted
- Unmask for user (toggle): Enable to restore original values in responses
- Placeholder Format: Format for temporary placeholders (e.g.,
<{TYPE}_{COUNT}>)
Example Redact Pattern (without unmasking):
Pattern: \b\d{4}[\s-]?\d{4}[\s-]?\d{4}[\s-]?\d{4}\b
Severity: High
Redact String: [CREDIT_CARD_REDACTED]
Reason: Credit card numbers should be redacted from logs
Unmask for user: OFFExample Redact Pattern (with unmasking):
Pattern: \b[A-Za-z0-9._%+-]+@[A-Za-z0-9.-]+\.[A-Z|a-z]{2,}\b
Severity: Medium
Redact String: [EMAIL_REDACTED]
Reason: Email addresses should be hidden from LLM provider
Unmask for user: ON
Placeholder Format: <{TYPE}_{COUNT}>When "Unmask for user" is enabled:
- Sensitive data is masked with placeholders (e.g.,
<EMAIL_1>) before sending to LLM provider - Original values are stored securely
- Response is automatically unmasked before returning to user
Add/Remove Patterns:
- Click + Add Redact Pattern to create a new pattern
- Click Remove to delete a pattern
Organization-Specific Pattern Examples
Use these examples as starting points for your custom rules.
Employee Information Detection
In Policy Builder → Security Rules:
Rule ID: COMPANY_001
Name: Employee ID Detection
Category: Data Protection
Severity: Medium
Description: Detect company employee ID patterns
Patterns:
\b(EMP|EMPL)[-_]?\d{6}\b
\b[A-Z]{2}\d{6}\b
\bSTAFF[-_]?\d{4,8}\bAPI Key Protection
In Policy Builder → Blocked Patterns:
Pattern: \bCOMP[-_]?[A-Za-z0-9]{32,64}\b
Severity: Critical
Action: block
Reason: Company API keys must never be exposedIn Policy Builder → Redact Patterns:
Pattern: \byour[-_]?api[-_]?[A-Za-z0-9]+\b
Severity: High
Redact String: [API_KEY_REDACTED]
Reason: API keys should be redacted from logs
Unmask for user: OFFInternal System Protection
In Policy Builder → Blocked Patterns:
Pattern: /internal/
Severity: High
Action: block
Reason: Access to internal systems blockedPattern: /admin/company/
Severity: High
Action: block
Reason: Company admin endpoints are restrictedPattern: /api/v[0-9]+/internal
Severity: High
Action: block
Reason: Internal API endpoints blockedFinancial Data Protection
In Policy Builder → Redact Patterns:
Pattern: \b\d{4}[-\s]?\d{4}[-\s]?\d{4}[-\s]?\d{4}\b
Severity: Critical
Redact String: [CREDIT_CARD_REDACTED]
Reason: Credit card numbers must be redacted for PCI compliance
Unmask for user: OFFPattern: \b\d{3}-\d{2}-\d{4}\b
Severity: Critical
Redact String: [SSN_REDACTED]
Reason: Social Security Numbers must be protected
Unmask for user: OFFPattern: \b[A-Z]{2}\d{2}[A-Z0-9]{4}\d{7}([A-Z0-9]?){0,16}\b
Severity: High
Redact String: [IBAN_REDACTED]
Reason: IBAN numbers must be redacted
Unmask for user: OFFProject and Customer Codes
In Policy Builder → Security Rules:
Rule ID: COMPANY_004
Name: Project Code Detection
Category: Data Classification
Severity: Low
Description: Track project codes in requests
Patterns:
\b(PROJ|PROJECT)[-_]?[A-Z]{2,4}[-_]?\d{3,6}\b
\b(CUST|CUSTOMER)[-_]?\d{6,10}\b
\b(CONTRACT|CNTR)[-_]?[A-Z0-9]{6,12}\bTesting Your Policy
Validate Policy Structure
Before saving:
- In the Policy Builder, click Validate button
- Review validation results for:
- Missing required fields
- Invalid regex patterns
- Duplicate rule IDs
- Fix any errors before saving
Test Against Sample Content
After saving:
- Navigate to Policies → Policy Testing tab
- Select your custom policy from the dropdown
- Enter test content in the text area:
- Sample employee IDs:
EMP123456,AB987654 - Sample API keys:
COMP_abc123def456 - Sample internal URLs:
/internal/data
- Sample employee IDs:
- Click Test Policy
- Review detection results:
- Which patterns matched
- Severity levels assigned
- Actions that would be taken (block/monitor/redact)
Test Pattern Matching
Test individual patterns:
- In Policy Testing, enter sample data that should match your patterns
- Verify patterns are detected correctly
- Check that severity levels are appropriate
- Ensure redaction strings are applied correctly
Example test content:
Employee EMP123456 accessing /internal/data
Project PROJ-ABC-001234 with API key COMP_abc123def456
Customer CUST123456789 with credit card 4532-1234-5678-9010Test Redaction and Unmasking
For redact patterns with unmasking enabled:
- Create a test proxy with your policy
- Send a request containing sensitive data
- Check proxy logs to verify:
- Data was masked before sending to LLM provider
- Response contains unmasked data for the user
- Placeholder format is correct (e.g.,
<EMAIL_1>)
Deploying Your Custom Policy
Apply to New Proxy
- Navigate to MCP Security or LLM Security page
- Click + Create Proxy
- Fill in proxy details (name, target, port)
- In Policy Selection, find your custom policy
- Select your custom policy (checkbox)
- Click Create
Apply to Existing Proxy
- Navigate to Proxies page
- Find your proxy and click Edit
- Scroll to Policy Assignment section
- Select your custom policy
- Click Save
Combine with Default Policies
You can use your custom policy alongside default policies:
- In proxy creation/editing, select multiple policies:
- Your custom policy:
acme-corp-security - Default policy:
llm-critical-security - Data protection:
llm-data-redaction
- Your custom policy:
- All selected policies are applied to the proxy
- Policies work together for defense-in-depth
Managing Custom Policies
View Your Policies
- Navigate to MCP Security or LLM Security page
- Your custom policies appear in the policy list
- Look for policies with your custom names
Edit a Custom Policy
- Navigate to MCP Security or LLM Security page
- Find your custom policy card
- Click Edit button
- Policy Builder opens with current settings
- Make your changes
- Click Validate, then Save Policy
Delete a Custom Policy
- Navigate to MCP Security or LLM Security page
- Find your custom policy card
- Click Delete button
- Confirm deletion
- Policy is removed from all proxies using it
Enable/Disable a Policy
- Find your policy card
- Use the Enable/Disable toggle
- Disabled policies remain configured but are not applied
Policy Best Practices
- Start with Templates: Use templates as starting points rather than building from scratch
- Use Pattern Library: Leverage pre-built patterns for common detections (PII, toxicity, injection)
- Test Thoroughly: Always test policies in the Policy Testing tab before deployment
- Start with Monitoring: Set initial policies to "monitor" or "log" actions, then gradually enable blocking
- Version Your Policies: Use the version field to track policy changes over time
- Document Patterns: Use descriptive rule names and detailed reasons for each pattern
- Review Regularly: Check policy performance in the Performance tab and adjust as needed
- Combine Wisely: Use 2-4 complementary policies per proxy for balanced protection
Understanding Pattern Actions
Blocked Patterns (Immediate Rejection)
Use for:
- Malicious patterns (SQL injection, command injection)
- Known attack signatures
- Patterns that indicate active threats
Result:
- Request is immediately rejected
- Error returned to client
- Alert created in system
Redact Patterns (Replace and Allow)
Use for:
- Sensitive data that needs logging but should be masked
- PII that must be redacted for compliance
- Secrets that shouldn't appear in logs
Result:
- Pattern is replaced with redact string
- Request continues with redacted content
- Original content recorded in secure logs (if enabled)
Redact with Unmasking (Mask from Provider, Show to User)
Use for:
- Protecting user data from LLM providers
- Maintaining user experience while ensuring privacy
- Compliance with data minimization requirements
Result:
- Pattern masked with placeholder before LLM provider
- LLM processes masked content
- Response automatically unmasked before returning to user
- User sees original data, LLM provider does not
Troubleshooting
Policy Not Appearing in List
Check:
- Policy was saved successfully (check for success notification)
- Policy type matches page (MCP policies on MCP page, LLM on LLM page)
- Refresh the page to reload policy list
Patterns Not Matching
Check:
- Use Policy Testing tab to test patterns individually
- Verify regex syntax using the Validate button
- Ensure patterns are properly escaped (use raw strings)
- Test with actual sample data that should match
Policy Validation Errors
Common issues:
- Invalid regex: Test patterns with an online regex tester
- Missing required fields: Ensure Policy Name and Type are filled
- Duplicate Rule IDs: Each rule must have a unique ID
Policy Performance Issues
Solutions:
- Avoid overly complex regex patterns
- Use specific patterns instead of broad catch-alls
- Check Performance tab for slow patterns
- Consider splitting large policies into multiple focused policies
Need Help?
- Policy Overview: See Policy Overview Guide to understand default policies
- Pattern Library: Navigate to Policies → Pattern Library tab for pre-built patterns
- Templates: Navigate to Policies → Templates tab for policy templates
- Testing: Use Policies → Policy Testing tab to validate before deployment
- Performance: Check Policies → Performance tab for optimization insights
Summary: Creating Custom Policies
The AI Security Gateway provides three flexible ways to create custom policies:
- Templates - Start with pre-configured policies and customize for your needs
- Pattern Library - Add proven detection patterns to new or existing policies
- Policy Builder - Build completely custom policies from scratch
All policy management is done through the intuitive web interface - no file editing or command-line tools required.
Key Features:
- Visual Policy Builder with validation and testing
- Pre-built Pattern Library for PII, Toxicity, and Injection detection
- Redaction with Unmasking to protect data from LLM providers while maintaining user experience
- Real-time Testing to validate policies before deployment
- Flexible Deployment to apply policies to multiple proxies
Security policies should be tailored to your specific organizational needs and threat model. Use the tools provided to create, test, and deploy policies that protect your unique environment.